Ransomware is one of the organizations’ most costly and high-profile cyber threats today. It can cripple entire systems, forcing businesses to take operations offline until a payment is received.
It’s a best practice for business owners to back up data regularly so that it can be restored in the event of a ransomware attack.
Phishing Campaigns
The first step in every phishing attack is gaining a victim’s trust. Attackers might use email spoofing, domain spoofing, and other fraudulent digital assets to impersonate a company or person to collect sensitive data from the unsuspecting target.
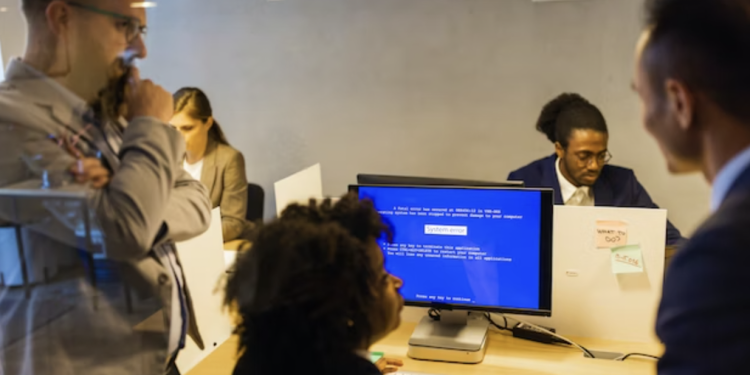
Once the attacker has obtained a victim’s information, they can use it for many different purposes. They may use it to steal access credentials for a website or online account, obtain permissions to modify and compromise connected systems (such as point-of-sale terminals), or even hijack entire computer networks until a ransom payment is delivered.
Attackers also might incorporate unique tactics to make their phishing schemes more effective. For example, suppose an attacker is targeting a call center employee. In that case, they might employ the “mumble technique,” in which the attacker will mumble when asked questions to sound like a normal human being. Another common tactic is impersonating in-house tech support and using technical jargon to convince victims they are legitimate. As the COVID-19 pandemic drove more employees to work remotely, attacks such as this increased.
Targeted Attacks
Over the past few years, ransomware attackers have shifted from opportunistic to targeted attacks. These attacks focus on specific victims and go to great lengths to learn about their systems and identify sensitive data. Cybercriminals then encrypt that data and hold it, hostage until the victim pays a ransom. These attacks are more resourceful than opportunistic attacks and can be paired with other tactics like DDoS, data theft, or dark web leaks. Some threat groups have even started layering extortion techniques to put more pressure on the victims of the attack. For example, the hacker group recently attacked Pipeline and demanded a ransom to decrypt their data. In addition to encrypting their information, they threatened to release the victim’s data on the dark web and launch a DDoS attack against them.
Targeted common ransomware attacks are also used to infect critical infrastructure systems and can be delivered via USB devices. They can then spread to other systems on the network that are not connected to the Internet. Monitoring your existing security solutions and networks is essential to see if the malicious actors have already been detected.
Double Extortion
Double and triple extortion attacks have helped to elevate ransomware from an encryption-based threat to a multifaceted cybercriminal enterprise. It logged 470 million ransomware attacks in the third quarter of 2021, more than double the number detected in the same period in 2019.
Malicious actors encrypt production data and data backups, then exfiltrate (steal) that data from victim systems and threaten to publicly release it online or sell it on the dark web if victims don’t pay their demanded ransom. This unique attack tactic emerged in 2019 and was later adopted by other ransomware families.
Thorough training is essential to help employees understand how to spot double extortion attacks and what steps they should take to avoid facilitating such an attack. Implementing an anti-trust architecture that prevents hackers from moving laterally through your servers will reduce the likelihood of double extortion ransomware attacks.
DDoS Attacks
A ransomware attack is not only financially devastating for victims (inflation, lost productivity, IT costs, legal fees, credit monitoring services, and the payment of the ransom itself), but it can also expose confidential or proprietary information and leave a business with a tarnished reputation. Cyber threat actors may threaten to leak this information publicly or sell it on the Dark Web if they are not paid the demanded sum.
Most ransomware attacks are opportunistic, disseminated via common infection vectors like spam email and compromised websites. However, in some cases, a cybercriminal will intentionally target a victim through social engineering. The malware, for example, was widely used to target schools and hospitals for a higher chance of receiving the requested ransom payment.
DDoS attacks leverage “botnets” of malware-infected devices to flood a server with spurious connection requests to overwhelm its processing capacity and bring it offline. Screen lockers – the most popular type of ransomware – also use this technique to prevent users from accessing a device or system until a ransom is paid.
Social Engineering
It doesn’t matter if you have locks, deadbolts, alarm systems, guard dogs, and armed security personnel; you are the weakest link in your company’s security chain. Attackers are preying on your naivety to compromise your business.
These attacks can take many forms, from posing as a tech-support professional or a delivery person to emailing you with an attachment that looks like a company document. Or, they can use a technique known as tailgating, where an attacker, without the proper authentication, follows an authenticated employee into a secure area to bypass security mechanisms.
As ransomware attacks grow increasingly targeted and more sophisticated, attackers are experimenting with various strategies to gain access and cause the most damage. A recent report found that some ransomware attackers are layering extortion techniques to maximize their attacks’ impact. This includes stealing sensitive data, encrypting files, and threatening to leak them online. This method of exploitation is growing in popularity as more attacks involve double extortion — a trend that has grown year over year.